Polymorphic Virus
Definition
What is a polymorphic virus? A polymorphic virus is a complex computer virus that can adapt to the various defenses you impose. It can constantly create modified versions of itself to avoid detection but retain the same basic program after each infection. In order to change its physical file composition during each infection, the polymorphic virus encrypts its code and adopts a different encryption key each time.
Each time a polymorphic virus infects a computer, it relies on the mutation engine to change its decryption routine. In this way, traditional security solutions may not easily capture them in that they do not use static, unchanged code. The use of complex mutation engines generates billions of decryption routines, which makes them unrecognizable by many detection techniques.
This type of “shape shifting” virus will generate malicious code, and these malicious codes will continue to copy itself and repeatedly change its characteristics in order to escape and surpass the computer’s defenses, and ultimately damage the system.
This feature prevents signature-based detection solutions from identifying the file as malicious. Even if a new signature is identified and added to the signature database of the antivirus solution, the polymorphic malware can continue to change the signature and attack without being discovered.
Webroot research shows that almost all viruses today contain polymorphism. And when combined with other malicious programs, polymorphic viruses pose a greater risk to their victims.
Related post: What Is a Macro Virus and How to Prevent It on Windows 10?
Spreading Method
Polymorphic viruses are usually spread through spam, infected sites, or through the use of other malware. Any Internet or email activity will put you at risk.
For example, when you visited a free software site to download software for free but did not realize that it was not a legitimate website, you clicked some links before leaving the website. You may even click on pop-up ads that look completely harmless, but these ads are likely to be infected with the polymorphic virus.
Examples
There are some polymorphic virus examples, which have been listed below:
Storm Worm Email
The infamous spam email sent in 2007 with the theme “230 dead as storm batters Europe” caused 8% of malware infections worldwide. After opening the attachment of the email, the malware installs the wincom32 service and Trojan on the recipient’s computer, thereby turning it into a bot. One of the reasons why it was difficult to detect storm worms using traditional antivirus software was that malicious code used every 30 minutes or so will be tampered with.
CryptoWall Ransomware
As polymorphic ransomware, CryptoWall encrypts files on the victim’s computer and requires a ransom to decrypt it. The polymorphic builder used in Cryptowall is used to develop essentially new variants for each potential victim.
VirLock
In addition to locking the computer screen of the host computer like traditional ransomware, VirLock can also infect files, replicate itself and change the format.
Related post: How to Prevent Ransomware? 7 Tips to Prevent Ransomware
How to Know If Your Computer Is Infected with Polymorphic Virus?
Since polymorphic viruses can appear in almost any form of virus, you need to pay close attention to the computer and what it displays. When the following phenomena appear on your computer, your computer may be infected with the polymorphic virus.
- The system suddenly slowed down. Maybe you need this post – 13 Tips to Windows 10 Very Slow and Unresponsive [2020 Update].
- The computer issued a strange request: a request to enter a password or sensitive information. Maybe you need this post – Configure Windows 10 from These 3 Aspects to Protect Your Privacy.
- A web browser suddenly takes you to a website you don’t need, or a pop-up ad occupies the screen on a website that doesn’t normally use these types of ads.
- Blue screen of death.
- The computer may not allow you to access the files and documents you need. Maybe you need this post – It’s Easy to Fix Access Is Denied (Focus on Disk and Folder).
Thousands of viruses are released every day, so if you find something strange, please use anti-virus software for additional checks.
How to Get Rid of the Polymorphic Virus?
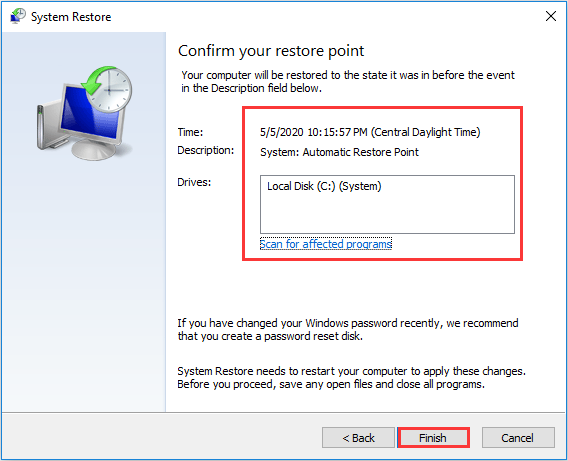
If you have created a system image before your computer is infected with the polymorphic virus, then you can try to run System Restore to get rid of the polymorphic virus. But when using this method, you need to be 100% sure that this restore point is not infected with the polymorphic virus.
Follow the simple guide to perform the System Restore:
Step 1: Press the Win + R keys at the same time to open the Run box.
Step 2: Type rstrui in the box and press Enter to open System Restore.
Step 3: Click Next, choose a restore point from the list and then click Next again.
Step 4: Confirm your restore point and then click Finish. Click Yes. Then wait for the process to complete.
Step 5: Reboot your PC to see if the problem is resolved.
If you haven’t created a system restore point, then you should reinstall your Windows system.
How to Prevent the Polymorphic Virus?
- Keep Your Software up to Date
- Never Click Suspicious Links or Attachments
- Update Your Defenses
- Use Heuristic Scanning
- Use Behavior-based Detection
- Back up Your Data Regularly
How to Prevent the Polymorphic Virus?
After getting some basic information about the polymorphic virus, then you may want to find some methods to prevent it. Here are multiple methods offered for you.
Method 1: Keep Your Software up to Date
It is pretty important to keep your software up to date. Although hackers will continue to update and refine the codes designed to destroy defects and vulnerabilities in operating systems and software, companies that own these systems are committed to fixing any defects and vulnerabilities that may arise.
Enterprise software manufacturers such as Microsoft, Oracle, and Adobe regularly release software updates that contain critical security patches for known vulnerabilities.
Method 2: Never Click Suspicious Links or Attachments
There could be malicious links or attachments used to spread malware in phishing emails or other unsolicited electronic communications. If you receive any emails that look suspicious, please send them directly to the recycle bin.
Method 3: Update Your Defenses
Another way to prevent the polymorphic virus is to ensure that you have the correct type of security solution software. A high-quality antivirus solution has advantages over the basic version, especially the ability to deploy a wider range of scanning technologies, tools, and algorithms to identify and respond to a wider range of threats. It also prevents various potential vulnerabilities that may provide access to the system, such as email attachments and Internet downloads.
For malware, time is of the essence, and advanced antivirus software can scan the system faster, allowing you to quickly take steps to eliminate or quarantine threats and repair or restore infected files.
Method 4: Use Heuristic Scanning
Heuristic scanning can prevent polymorphic viruses, but only if the polymorphic viruses consist of old malware code. Because heuristic scanning is not looking for something that exactly matches the identified threat, but looking for possible key components that threats might share, increasing the chance of discovering and preventing new variants of the virus. However, malware that has never been seen before will not be considered harmful.
Method 5: Use Behavior-based Detection
The preferred method of defense against polymorphic malware is to use tools that can identify and deal with threats based on their behavior rather than try to analyze their encoding. Antivirus software with endpoint detection and response or advanced threat detection is worth investing in.
Method 6: Back up Your Data Regularly
Prevention is the key, so you should back up your important files regularly. Even if your computer is infected with the polymorphic virus, the data that you backed up before will remain safe. Then how to do that? It is recommended to use MiniTool ShadowMaker, which is a powerful backup tool for Windows.
It supports backing up your files, folders, disks, partitions, and Windows operating systems. You can also use it to sync your files to other places and clone your hard drive to another for disk upgrade.
This tool also supports automatic backup and incremental & differential backup. What’s more, MiniTool ShadowMaker provides you a Trial Edition that you can use it for free within 30 days.
MiniTool ShadowMaker TrialClick to Download100%Clean & Safe
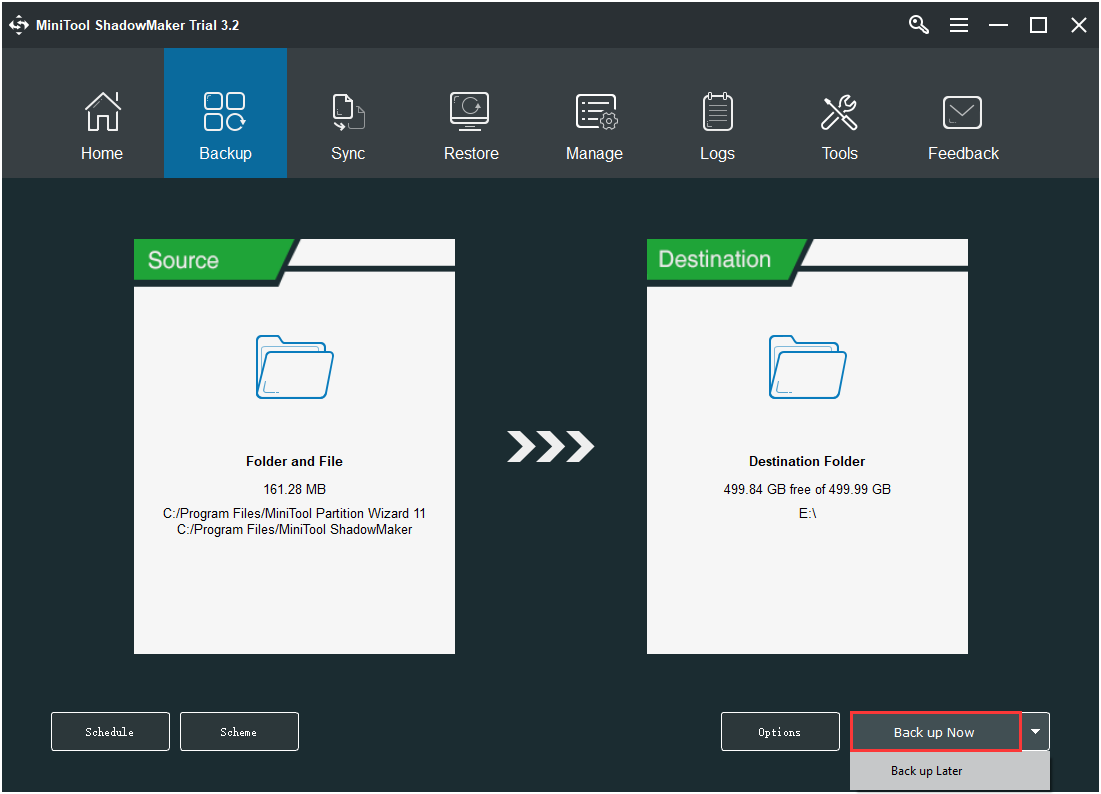
Follow the steps below to back up your important files on your computer:
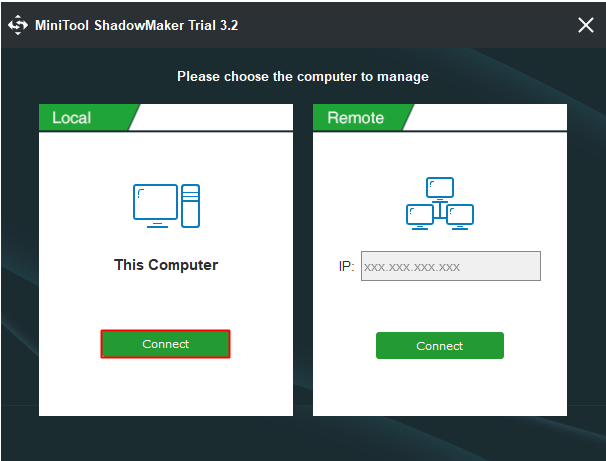
Step 1: Install and run MiniTool ShadowMaker, then click Keep Trial.
Step 2: Choose Connect under This Computer to get into the main interface.
Step 3: Go to the Backup page, choose backup source and backup destination (USB drive, external hard drive, etc.). By default, MiniTool ShadowMaker backs up the system.
Step 4: After you have confirmed the backup source and destination, then click Back up Now to start to back up your files. You can also delay the task by clicking Back up Later.
Final Words
To sum up, this post has introduced the polymorphic virus definition, spreading method, and some examples. In addition, you can find several ways to prevent polymorphic viruses from infecting your computer.
If you have any confusion about the methods or have any better advice, leave a comment below or send an email to [email protected], we’ll reply to you as soon as possible.
Polymorphic Virus FAQ
- Viruses are attached to files or programs, and it only affects when the file or program is running. Almost all viruses are attached to executable files.
- Worms are a subclass of viruses. The worm uses the file or information transmission feature on your system, which allows the worm to run independently.
User Comments :