What Is Ransomware
Whatis ransomware? A ransomware attack is a malware attack that encrypts the user’s data and blocks access until a ransom is paid. Ransomware attackers often use social engineering techniques such as phishing to gain access to a user’s environment.
Related article:
- The Popular Types Of Computer Virus You Should Know
- The Different Types of Malware and Useful Tips to Avoid Them
Types of Ransomware
Nowadays, two types of ransomware are very prevalent – Locker ransomware and Crypto ransomware. Then, we will introduce detailed information about them.
1. Locker Ransomware
This type of malware blocks basic computer functions. For example, you may be denied access to the desktop, while the mouse and keyboard are partially disabled. This allows you to continue interacting with the window containing the ransom demand for payment. Besides, your computer won’t work.
2. Crypto Ransomware
The purpose of Crypto ransomware is to encrypt your important data, such as documents, pictures, and videos, without interfering with the basic functions of your computer.
Crypto ransomware hackers often add a countdown to their ransom demands – If you don’t pay the ransom by the deadline, all your files will be deleted. Since many users don’t know the need to store their important data in the cloud or on an external physical storage device to make backups, this type of ransomware can cause their files to be lost.
In addition to the common ransomware, there are some other types of ransomware. We will introduce them one by one.
3. WannaCry Ransomware
WannaCry is the most widely known ransomware variant in the world. WannaCry has infected nearly 125,000 organizations in more than 150 countries. Some alternative names for the WannaCry ransomware are WCry or WanaCrypt0r.
Users are locked and demanded to pay a ransom in Bitcoin. The attack exposed outdated systems as hackers exploited an operating system vulnerability that had been patched at the time of the attack. The global economic damage caused by WannaCry is approximately $4 billion.
Also see: How to Protect Yourself against WannaCry Ransomware
4. Locky
Locky encrypts more than 160 file types and spreads via fake emails with infected attachments. Users fell into an email scam and installed ransomware on their computers. This method of spreading is called phishing. Locky ransomware targets file types frequently used by designers, developers, engineers, and testers.
5. Ryuk
Ryuk is an encryption trojan that was spread in August 2018 that disables the recovery feature of the Windows operating system. This makes it impossible to restore encrypted data without an external backup. Ryuk also encrypts network hard drives.
6. CryptoLocker
CryptoLocker is ransomware first discovered in 2007 and spread through infected email attachments. Ransomware searches for important data on infected computers and encrypts it. An estimated 500,000 computers were affected.
7. Petya
Petya is a ransomware attack that occurred in 2016 and was resurrected as GoldenEye in 2017. Rather than encrypting certain files, the malicious ransomware encrypts the user’s entire hard drive. It encrypts the Master File Table (MFT), which makes the files on the hard drive inaccessible.
8. Bad Rabbit
Bad Rabbit was a 2017 ransomware attack that spread through so-called drive-by attacks. Insecure websites are used for attacks. In a drive-by ransomware attack, a user visits a real website without knowing it has been hacked. For most drive-by attacks, the user simply calls the page attacked in this way.
However, in this case, running an installer that contains disguised malware can lead to an infection. This is called a malware dropper. Bad Rabbit asks users to run fake Adobe Flash installations, then, the computer will be infected.
9. Jigsaw
Jigsaw is a ransomware attack that started in 2016. The attack takes its name from the image it shows of the famous puppet from the Saw movie series. Every hour, if you still haven’t paid the ransom, Jigsaw ransomware will delete more files.
10. B0r0nt0k
B0r0nt0k is specifically targeting Windows and Linux-based servers. This ransomware encrypts the files of the Linux server and appends the “.rontok” file extension. Not only does this malware threaten files, but it also changes startup settings, disables features and applications, and adds registry keys, files, and programs.
Also see: What Is PXJ Ransomware and How to Remove It?
How to Recover Your Data
If you find that your system is infected by ransomware and data is deleted by ransomware and there is no backup available, you had better try the data recovery tool first. Therefore, you can try the free version of MiniTool Power Data Recovery.
MiniTool Power Data Recovery provides you with a reliable and quick data recovery solution to recover the original data which is deleted by the ransomware. Let’s see how to recover the deleted data with this powerful tool.
Step 1: Download and install MiniTool Power Data Recovery. Launch it.
MiniTool Power Data Recovery TrialClick to Download100%Clean & Safe
Step 2: All the detected partitions are listed here by drive letter, you can select a partition and click Scan.
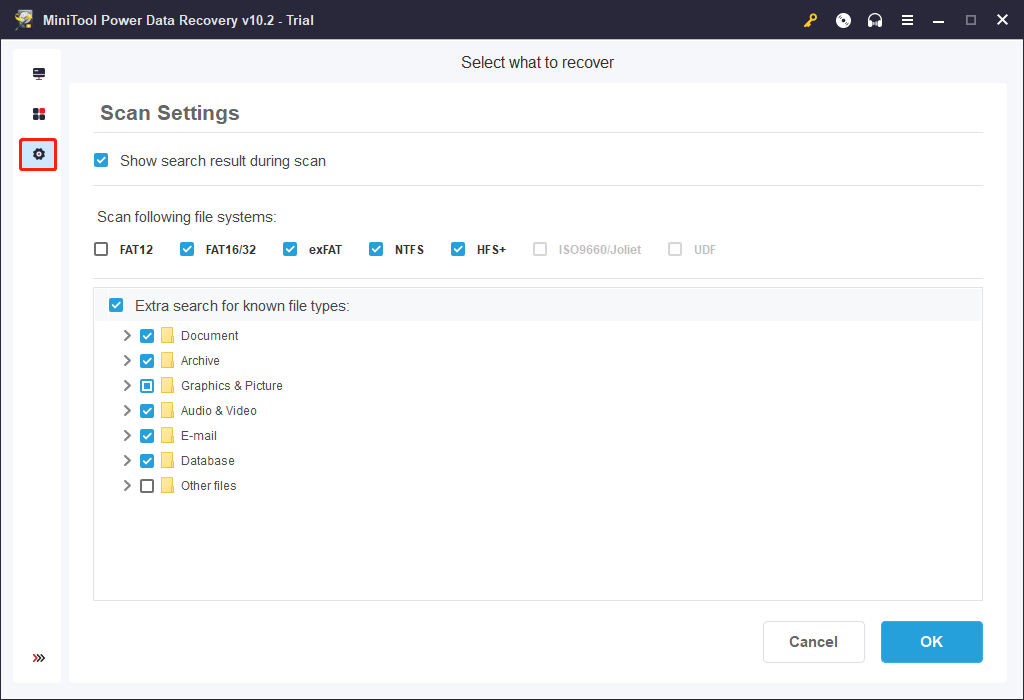
Step 3: This program is scanning the lost partition. You can click the Stop or Pause button to stop or pause the scanning process.
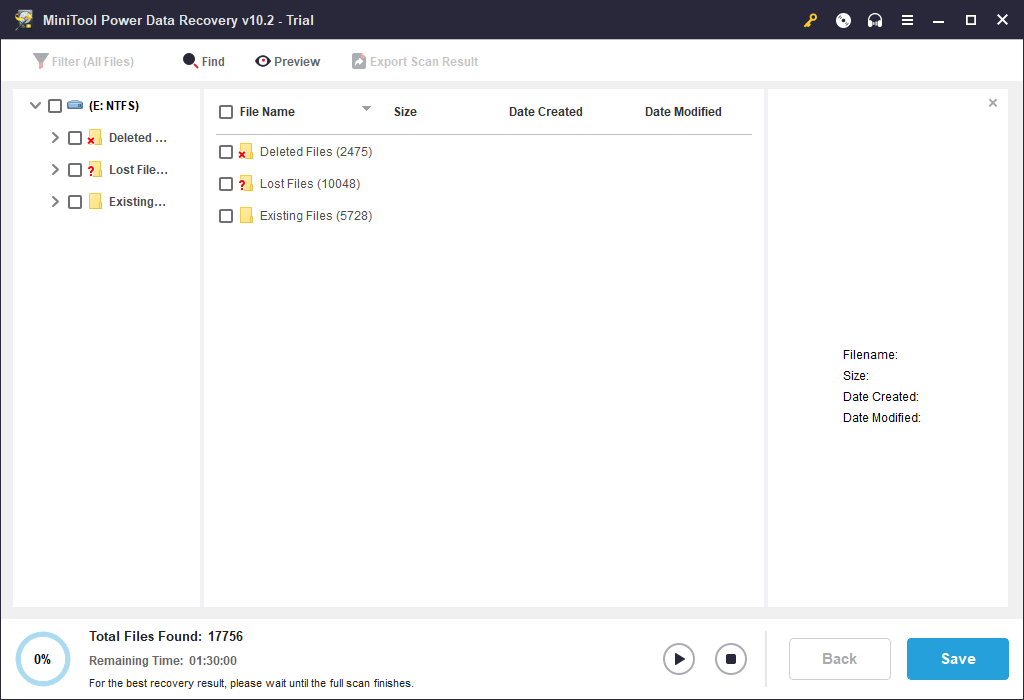
Step 4: After completing the scan, you can check some items and click the Save button. Two options can help you to find needed data quickly: Filter(All Files), Find.
- Filter: This Filter option can help you to search files by filename, file size, creation date, and other features. Furthermore, this program shows deleted, lost, or normal files based on needs.
- Find: Click the Find button, you can type the file name to find the specified file quickly. There are two options to the input file name. Match Case means you should note the uppercase and lowercase letters of the file name. Match Word means you should input the full file name accurately.
Step 5: In the pop-up window, select a directory to save selected files and click OK. Here, it is suggested that you choose another hard drive to save the recovered since the lost/deleted data could be overwritten.
Also see: How to Perform Ransomware Recovery and How to Protect Your Data
How to Avoid Different Types of Ransomware
Then, I will introduce how to avoid different types of ransomware.
- Never open, click or download content that you think is too suspicious, such as files, advertisements, emails, etc.
- Keep firewall open that can be used to detect any suspicious activity. Maybe, you are interested in this post –Windows Firewall for Windows 10 and Its Great Alternative.
- Purchase, run, and regularly update anti-malware and anti-spyware software.
- Only connect to a secure Wi-Fi network. Connecting to public Wi-Fi may expose your device to potential harm.
- Update the operating system regularly.
- Install spam filters to prevent the possibility of infection on all devices.
- Change your password regularly and follow password best practices.
- Use a secure file-sharing solution. This post – Top 8 File Sharing Programs Windows 10 [2020 Update] is what you need.
- Back up your important data regularly.
How to Back up Important Data
Speaking of backing up data, there is a great backup software – MiniTool ShadowMaker for you. It is also a powerful tool to protect your Windows. It is an all-around and free backup software designed for Windows 11/10/8/7, providing you with a data protection & disaster recovery solution.
Now you can download and try MiniTool ShadowMaker Trial Edition to do the backup task.
MiniTool ShadowMaker TrialClick to Download100%Clean & Safe
Let’s see how to use MiniTool ShadowMaker to back up your files.
Step 1: Install and launch MiniTool ShadowMaker, then click Keep Trial.
Step 2: Go to the Backup page, click Source, and then select Folders and Files. Check all the files and folders that you need and then click OK.
Step 3: Click Destination and then choose the external hard drive as the destination to save the backup image. Click OK to save changes. You should notice that you should connect the external hard drive to your PC before the backup.
Step 4: After you have confirmed the backup source and destination, then click Back up Now to start to back up your files.
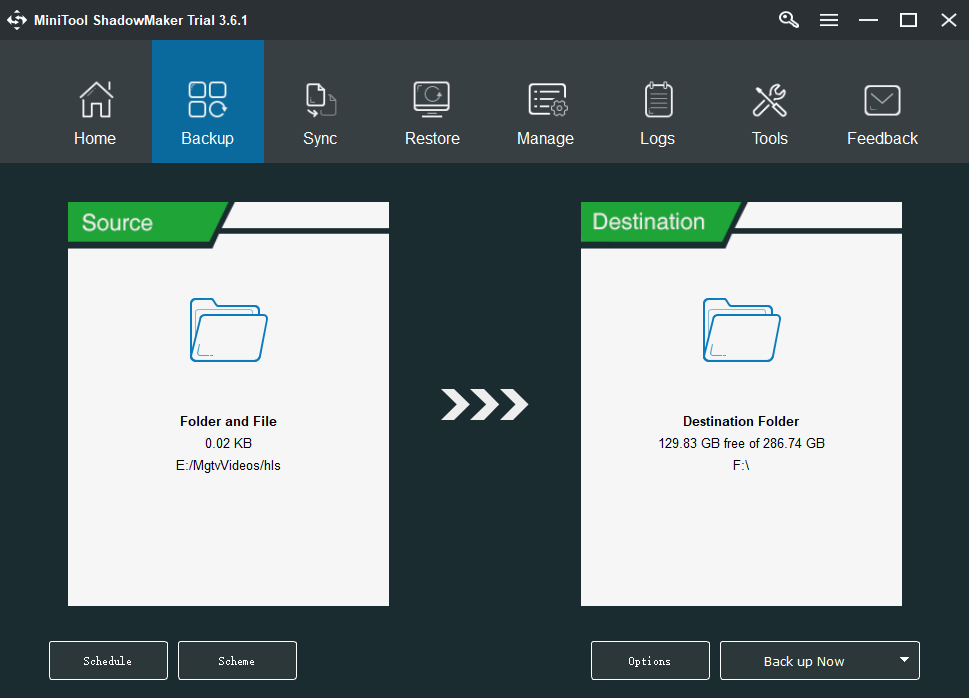
Then you just need to wait for MiniTool ShadowMaker to complete the process.
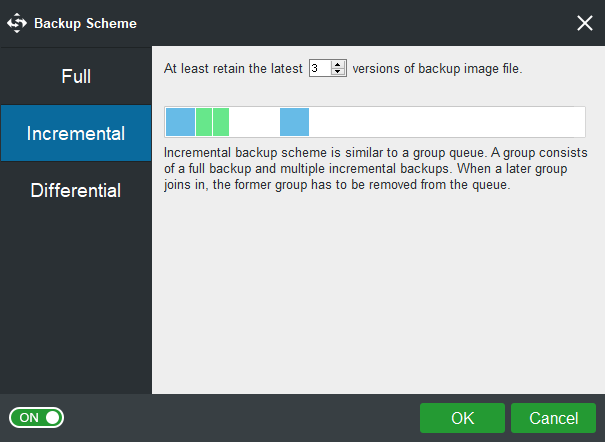
Besides backing up the files, this software can also be used to back up systems, folders as well as partitions. It is also a clone tool that can help you to clone the OS from HDD to SSD without data loss. So, besides creating a system image, you can also choose to clone the OS disk to another hard drive to get the Windows system without reinstalling.
MiniTool ShadowMaker also supports restoring Windows backup to a different PC with dissimilar hardware. This post – How Can You Do Windows Backup Restore to Different Computer can help you do that.
Bottom Line
This post has briefly shown you some basic information about the types of ransomware and you can know how to avoid it. Besides, this post also introduces you to two powerful programs – MiniTool ShadowMaker and MiniTool Power Data Recovery, which can help you back up data to protect it.
If you have any problems when you are using MiniTool software, please let us know. Or if you have any suggestions, also tell us. Sending an email to [email protected] or leaving a comment below is available.
User Comments :