Do you know what Dell Data Protection is? If you are a user of Dell devices, desktops or laptops, you are probably familiar with this solution. And, some other computer users may also hear of it.
In the past few years, from 2017 to 2021, different variants of Dell Data Protection got their end of life one by one. For example, Dell Data Protection | Endpoint Recovery came to end in October 2017; Dell Data Protection | Protected Workspace withdrew itself in January 2018; Dell Data Protection | Security Tools Mobile got ended in April 2018; Dell Data Protection | Cloud Encryption ended its life in May 2018; Dell Data Protection | Secure Lifecycle dropped out in November 2018; and Dell Data Protection | Encryption stopped in January 2021.
Besides the above completely ended products, Dell Data Protection | Security Tools has ended its support and Dell Data Protection | Mobile Edition has ended its maintenance.
- Dell Data Protection | Encryption was superseded by Dell Encryption in version 10.x and later.
- Dell Data Protection | Secure Lifecycle was the successor of Dell Data Protection | Cloud Encryption and it was replaced by Dell Data Guardian, which was sunset in late 2019.
What Is Dell Data Protection?
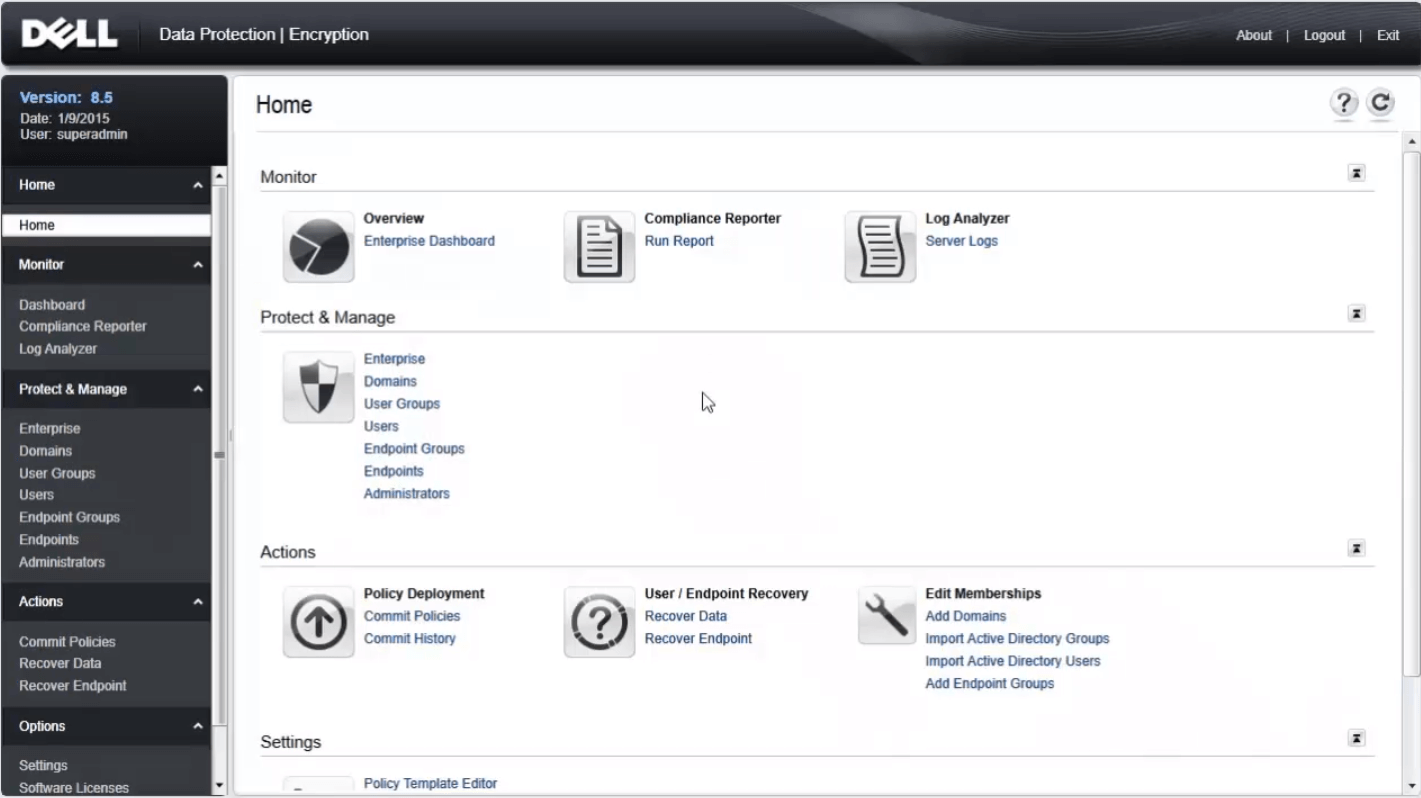
In general, Dell Data Protection is a multi-product solution focusing on data-at-rest encryption using a policy-driven file, folder encryption solution, self-encrypting drive management, as well as BitLocker management.
Dell Data Protection spans many products. It was originally named Credant Mobile Guardian. In 2012, Dell acquired Credant and rebranded the product to Dell Data Protection. In 2017, it was renamed Dell Data Security.
What Can Dell Data Protection Do?
Generally, Dell Data Protection can detect security risks, protect data, and manage data centrally on desktops, laptops, as well as external devices. It enforces access control policies, authentication, and encryption of sensitive data and makes use of collaborative tools integrated into existing user directories.
Dell Data Protection Features:
IT-friendly complete data protection
Implements encryption policies utilizing Software-based Data Centric Encryption, wherever the data locates. For mixed working environments, Dell Data Protection won’t interrupt current computer processes.
High-level protection
Exclusive to select Dell Precision systems, Dell Latitude, OptiPlex, and the optional Full Volume Encryption to give end-users high-level security. Relying on a Hardware Encryption Accelerator, Dell Data Protection offers a self-encryption-drive-like functionality without a drive size limit.
External Media Policies
The external media policies enforced by Dell Data Protection protect removable hard drives. Flexible policies and central management enable you to secure crucial data to your organization while allowing end-users to save personal data on external storage.
Manage Encryption
If you are using Dell Data Protection | Encryption Enterprise Edition, relying on its BitLocker Manager, you are able to get enterprise-level managing, auditing, and reporting capabilities from Microsoft BitLocker Drive Encryption on Windows 7 Enterprise and Ultimate editions.
Why Dell Data Protection Comes to Its End of Life?
As products pass their end of a potential, they are no longer useful to their users anymore. Or, when products become antiquated, they are sunset towards their end of life. Those products are probably substituted by other similar ones just like Dell Data Protection was replaced by Dell Encryption. Then, you may consider clear Dell Data Protection away from your machine.
How to Uninstall Dell Data Protection?
To remove Dell Data Protection, you need to rely on Dell Data Protection Uninstaller (Dell Data Security Uninstaller). Therefore, firstly, you need to download it from dell.com. Then, just follow the below steps.
1. Double-click on the downloaded DataSecurityUninstaller.exe file to launch it. Note that the file requires log4net.dll to locate in the same folder to run successfully.
2. When it asks “Do you want to allow this app to make changes to your device?”, if UAC (User Account Control) is enabled, just click Yes. If not, skip to the next step 3.
3. In the welcome screen, click Next to proceed.
4. It will select all the Dell security programs by default. If you want to keep some of them, just uncheck them from the list.
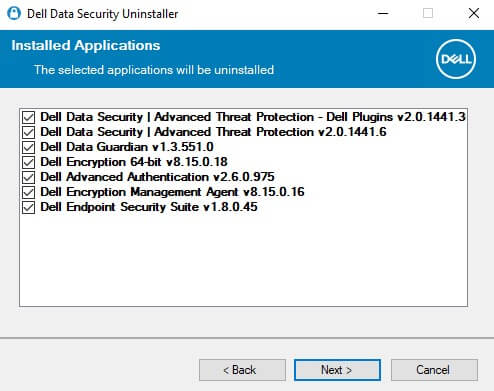
5. If Dell Data Protection Encryption Personal Edition or Dell Data Protection Encryption Enterprise Edition is present, proceed to step 6. Otherwise, skip to the below step 7.
6. In the Encryption Removal Agent Options user interface (UI), choose either of the below ones:
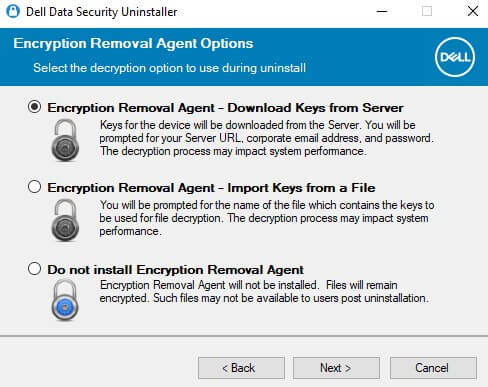
- Encryption Removal Agent – Download Keys from Server: Select this option, fill in the credentials of a Forensic Administrator for the listed Device Server, and continue with step 8.
- Encryption Removal Agent – Import Keys from a File: Choose this option, browse the location of the Forensic Downloaded File, enter the Passphrase for the file, and skip to step 8 once populated.
- Do Not Install Encryption Removal Agent: Pick this option and go directly to step 8.
7. If the self-encryption drive is provisioned on an endpoint, it must be deactivated before removing encryption. Click OK to exit the Dell Data Security Uninstaller. If a self-encryption drive is already deactivated or not used, just go to step 8.
8. Click Remove to delete the chosen software from step 4.
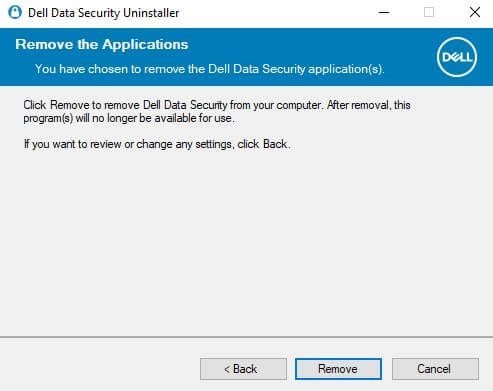
9. Click Finish to reboot your computer.
If any program fails to uninstall, it will appear in the Uninstall Logging tab.
Dell Data Protection Alternatives
Since Dell Data Protection has ended its services and its customers have to find other products to play its role in data protection. Below list some popular replacements of Dell Data Protection including the official Dell Encryption.
#1 Dell Encryption
Dell Encryption is nearly the same as Dell Data Protection. It inherits all the functions of Dell Data Protection and improves them to be better. This also means that Dell Encryption has some disadvantages that belong to Dell Data Protection. There are words on Dell official website states of that:
In many cases, for products that have reached End of Life, a newer product version may be required to resolve an issue if the current version exhibiting issues is End of Life.
Moreover, look at the history of Dell Data Protection-related programs and other security applications of Dell, it is a concern that maybe someday in the future, Dell Encryption will also go to the end of its life. Then, maybe another Dell replacement will take over your data security; maybe none. Until then, you must find another alternative. Then, why not now!
#2 BitLocker
BitLocker is a full volume encryption procedure embedded into Windows since Windows Vista. It is designed to achieve data protection by offering encryption for entire volumes. By default, it adopts the AES encryption algorithm in cipher block chaining (CBC) or XTS mode with a 128-bit or 256-bit key.
#3 MiniTool ShadowMaker
Unlike Dell Data Protection and Windows BitLocker, MiniTool ShadowMaker is a professional and reliable data backup software. Not only encryption can protect data, but also backup! The only difference is that encryption prevents data been seen and leaked while backup avoids data loss.
With MiniTool ShadowMaker, you can easily protect your important files/folders, system, applications, and so on. Below is a brief guide showing you how to make a backup of personal files.
Before start, you should download and install MiniTool ShadowMaker on your Dell devices. As long as you are running Windows systems, you are able to use it, no matter for PCs or Servers. MiniTool ShadowMaker also provides different editions for different users including Personal, Pro, and Business. You are recommended to download the below trial version, experience how useful MiniTool ShadowMaker is, and then upgrade to its standard version.
MiniTool ShadowMaker TrialClick to Download100%Clean & Safe
- Launch MiniTool ShadowMaker and click Keep Trial to continue.
- In its main UI, click Backup on its tab menu.
- In the Backup tab, click the Source module to select what you want to back up on your computer.
- Then, click the Destination module to choose where you would like to save the backup image. Here, an external storage device is recommended (e.g. USB flash drive).
- Finally, check the backup task and click Back up Now to start.
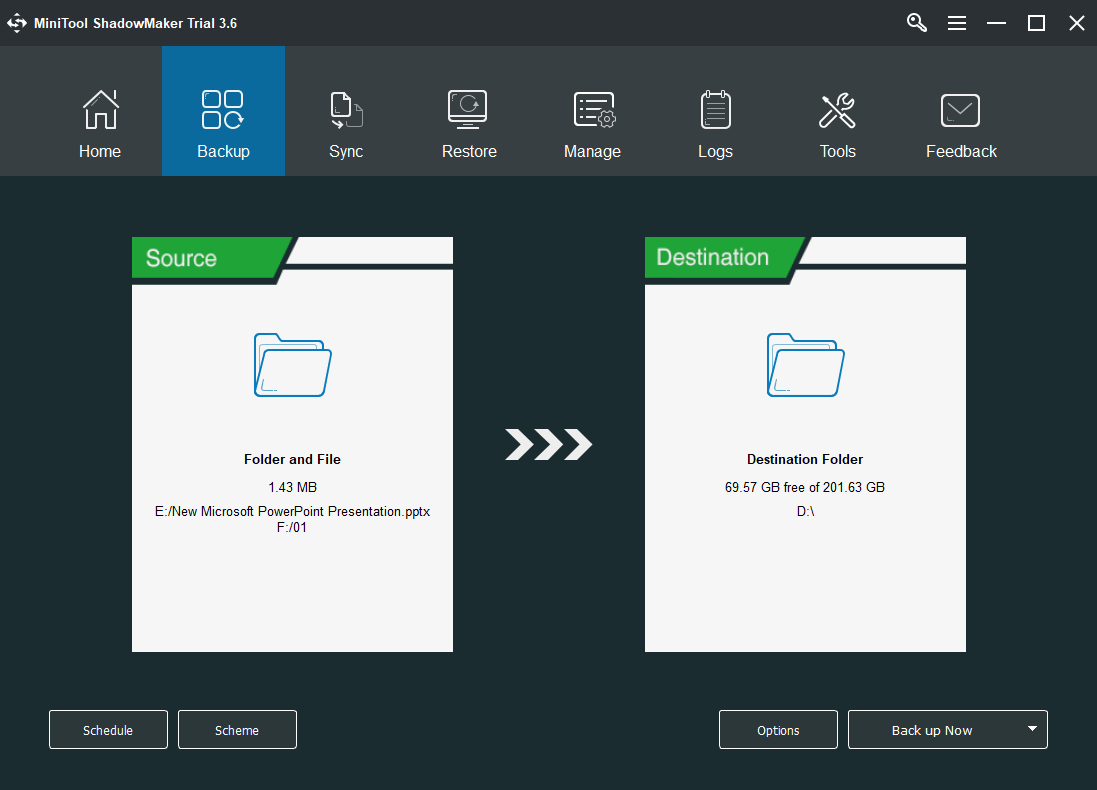
If you want to back up those personal data regularly and automatically in the future, you can rely on MiniTool ShadowMaker’s Schedule backup feature. Then, you should provide a large destination to save the coming image files. Don’t worry about the destination storage space, you can manage them by setting up a reasonable backup scheme to only save several latest images. Moreover, you can use either incremental backup or differential backup to only back up the changed contents of the source files.
OK, that is all about Dell Data Protection. Whether to continue with its successor Dell Encryption or switch to another encryption tool, or even ask help from backup solutions, it all depends on you! And, if you have anything want to say, just leave a message in below comment section. If you encounter any problem while using MiniTool ShadowMaker, feel free to contact us via [email protected].
Dell Data Protection FAQ
PowerProtect DD Series Appliances is designed with storage ranging up to 1.5 PB of physical or virtual storage (97.5 PB of logical storage), compute, and next-generation Data Domain deduplication technology.
PowerProtect DP Series Appliances is a converged solution that offers complete backup, replication, recovery, deduplication, instant access and restore, search and analytics, and seamless VMware integration, all in one appliance.
User Comments :